Bitcoin mining was invented as a mechanism to maintain trust in a system without central authority, ensuring that digital transactions could be verified and recorded transparently on a distributed network.
| Key Fact | Summary |
|---|---|
| Purpose | Mining provides decentralized trust: it verifies transactions, prevents double-spending, and mints new bitcoin without a central authority. |
| Consensus & Algorithm | Bitcoin uses Proof-of-Work with SHA-256, making blocks costly to produce but easy for the network to verify. |
| How a Block Is Mined | Miners gather transactions, build a block, and iterate a nonce until the block’s hash meets the network difficulty; the winning block is broadcast and validated by nodes. |
| Difficulty & Block Time | Difficulty retargets every 2,016 blocks (~2 weeks) to keep average block intervals near 10 minutes regardless of total hash rate. |
| Issuance & Incentives | Miner revenue comes from block rewards and transaction fees; block rewards follow a programmed halving schedule that steadily reduces new supply. |
| Hardware Evolution | Mining progressed from CPUs → GPUs → FPGAs → ASICs, with ASICs delivering orders-of-magnitude efficiency gains and enabling industrial-scale operations. |
| Energy Profile | Proof-of-Work entails significant electricity use; miners seek low-cost power (often hydro, geothermal, or excess renewables) to remain profitable. |
| Mining Pools | Most miners join pools to combine hash power and smooth income; rewards are shared proportionally to each participant’s contributed work. |
The Origins of Bitcoin Mining
When Bitcoin was introduced in 2009 by the pseudonymous creator Satoshi Nakamoto, the challenge was how to create a decentralized financial system where transactions could be validated without banks or governments. Mining emerged as the mechanism to solve this issue. It combined cryptography, distributed ledgers, and computational work to ensure that no single entity could manipulate the transaction record.
The Role of Mining in the Bitcoin Network
Mining serves two primary purposes: it secures the Bitcoin network against fraudulent transactions, and it releases new bitcoins into circulation. Without mining, the blockchain could not operate reliably, as there would be no process for achieving consensus among participants.
Transaction Verification
Every Bitcoin transaction must be confirmed before it becomes part of the permanent ledger. Miners verify these transactions, group them into blocks, and then compete to solve a mathematical problem that allows them to add the block to the blockchain.
Monetary Issuance
New bitcoins enter circulation through mining rewards. This mechanism ensures a predictable and gradually decreasing supply, following the programmed halving events. The design was intentional to mimic the scarcity of precious metals like gold.
How Bitcoin Mining Works
The process of mining combines cryptography, economics, and computing hardware. At its core, it is about finding a solution to a cryptographic puzzle, known as the Proof-of-Work (PoW).
Step-by-Step Process
- Pending transactions are broadcast across the network.
- Miners collect transactions into a block.
- The block is assigned a cryptographic hash target.
- Miners repeatedly adjust a value called the “nonce” to attempt to produce a hash that meets the difficulty target.
- The first miner to find a valid hash broadcasts the solution to the network.
- Other nodes verify the solution, and once validated, the block is added to the blockchain.
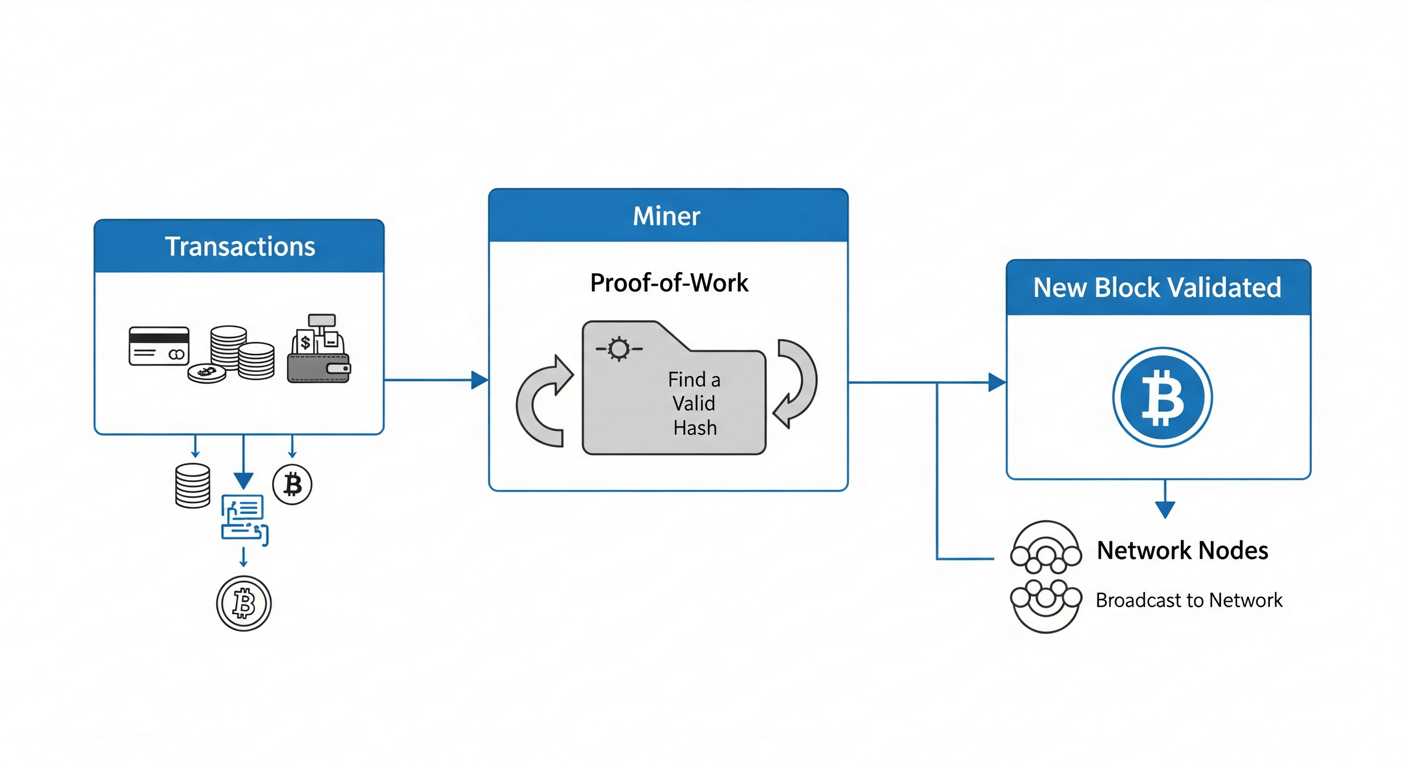
Proof-of-Work and Hash Functions
Mining depends on Proof-of-Work, a concept that requires participants to perform a measurable amount of computation. The algorithm used in Bitcoin is SHA-256 (Secure Hash Algorithm 256-bit). This ensures that solving the puzzle requires significant computational effort, while verifying the solution remains easy for other participants.
Why SHA-256?
The choice of SHA-256 was not accidental. It is widely used in cybersecurity applications and is considered robust against common attack methods. Its deterministic yet unpredictable output makes it ideal for mining, as miners must rely purely on computation rather than shortcuts.
Mining Difficulty and Adjustments
The Bitcoin network adapts to the total computing power by adjusting the difficulty of mining every 2,016 blocks (roughly two weeks). This ensures that blocks are added at an average rate of one every ten minutes, regardless of how much hardware is active on the network.
Difficulty Retargeting
If miners collectively produce blocks too quickly, the difficulty increases, requiring more computation. If mining slows down, the difficulty decreases, making it easier to find valid blocks again. This self-adjusting mechanism is essential for maintaining network stability.
Mining Hardware Evolution
From the early days of mining with laptops to today’s industrial-scale mining farms, hardware has undergone radical evolution. The progression reflects the growing difficulty of mining and the economic incentives driving efficiency.
Stages of Hardware Development
| Era | Hardware Type | Performance |
|---|---|---|
| 2009–2010 | CPU (Central Processing Unit) | Low efficiency, suitable for early Bitcoin mining |
| 2010–2012 | GPU (Graphics Processing Unit) | Massive improvement in hash rate, highly parallel |
| 2012–2013 | FPGA (Field Programmable Gate Array) | Lower power usage, moderate efficiency gains |
| 2013–Present | ASIC (Application-Specific Integrated Circuit) | Custom-built chips for SHA-256, extremely efficient |
Energy Consumption in Mining
Bitcoin mining is known for its significant energy demands. The constant need for computational work translates into high electricity usage. This has led to intense debates about sustainability and efficiency in the sector.
Global Energy Estimates
Studies have placed Bitcoin’s electricity consumption at levels comparable to entire countries. While figures fluctuate depending on hardware and geography, the pattern of growing consumption is undeniable.
Sources of Energy
Mining farms often seek low-cost electricity to remain profitable. Hydropower, geothermal energy, and excess renewable capacity are common choices. The concentration of mining in regions with affordable power illustrates the close relationship between mining economics and energy markets.
The Economics of Bitcoin Mining
Mining is not only a technical process but also an economic competition. Profitability depends on hardware efficiency, electricity costs, Bitcoin’s price, and the mining difficulty at any given time.
Block Rewards
Miners earn rewards for each valid block they add. Initially, this reward was 50 BTC per block. Every four years, a halving event reduces the block reward by 50%. As of today, the reward is 6.25 BTC per block, with the next halving expected to reduce it further.
Transaction Fees
In addition to block rewards, miners collect transaction fees from users. These fees incentivize miners to include transactions in blocks, especially when the network is congested.
Profitability Calculations
To calculate profitability, miners must consider hardware cost, electricity price, and the projected difficulty. Online calculators can help estimate potential earnings, but real-world factors such as cooling systems and operational expenses also play a critical role.
Mining Pools
Due to the competitive nature of mining, most miners today join mining pools. These pools combine the computational power of many participants, improving the chances of winning block rewards, which are then distributed proportionally among contributors.
How Mining Pools Work
Each participant contributes hash power to the pool. When the pool finds a valid block, the rewards are shared according to the share of computation contributed by each miner. This provides a more stable and predictable income stream compared to solo mining.
Geographical Distribution of Mining
Mining activity has shifted dramatically over the years. Initially concentrated in China due to cheap electricity, mining has since diversified after regulatory crackdowns. Today, mining operations can be found in North America, Central Asia, and parts of Europe.
Key Mining Hubs
- United States – leveraging natural gas and renewables
- Kazakhstan – coal-heavy but low-cost electricity
- Iceland – geothermal and hydro resources
The Mining Software Landscape
Software plays a crucial role in managing hardware, connecting to mining pools, and optimizing efficiency. Over time, specialized mining software has emerged, offering dashboards, monitoring tools, and advanced configurations.
Popular Mining Software
| Software | Platform | Main Features |
|---|---|---|
| CGMiner | Linux, Windows | Highly customizable, supports multiple hardware types |
| BFGMiner | Linux, Windows | Focus on FPGA/ASIC, modular architecture |
| NiceHash | Windows | User-friendly, allows hash power marketplace |
The Network Effects of Mining
Mining is more than just a technical function; it is an essential component of Bitcoin’s decentralized consensus. The act of miners competing to add blocks ensures that no single participant controls the ledger. This mechanism transforms individual incentives into collective security for the entire network.
Hash Rate as a Security Metric
The total computing power of the network, known as the hash rate, is often used as a measure of security. A higher hash rate means it becomes exponentially more difficult for any single entity to attempt a double-spending attack or rewrite parts of the blockchain.
Incentive Alignment
Miners invest heavily in hardware and electricity. Their economic incentive is to act honestly because attempting to attack the network would mean devaluing the very asset they are rewarded with. This alignment of incentives is central to Bitcoin’s resilience.
Block Structure in Mining
Every block mined in the Bitcoin blockchain follows a structured format. Understanding this structure helps explain why mining is both computationally intensive and cryptographically secure.
Block Components
- Block Header: Contains metadata such as version, timestamp, previous block hash, Merkle root, and difficulty target.
- Merkle Root: A cryptographic summary of all transactions in the block, ensuring integrity.
- Transactions: The individual Bitcoin transfers, including the coinbase transaction that rewards the miner.
The Coinbase Transaction
Each block includes a special transaction, known as the coinbase, which allows the miner to claim the block reward and any transaction fees. This is the only mechanism by which new bitcoins are introduced into circulation.
Halving Events and Scarcity
One of Bitcoin’s most distinctive features is its predetermined issuance schedule. Approximately every four years, the block reward is cut in half in an event known as the halving. This schedule creates digital scarcity, reinforcing Bitcoin’s narrative as “digital gold.”
Historical Halvings
| Year | Block Reward Before | Block Reward After |
|---|---|---|
| 2012 | 50 BTC | 25 BTC |
| 2016 | 25 BTC | 12.5 BTC |
| 2020 | 12.5 BTC | 6.25 BTC |
| 2024 | 6.25 BTC | 3.125 BTC |
The Role of Mining in Network Consensus
Mining is the backbone of Bitcoin’s Proof-of-Work consensus. By solving cryptographic puzzles, miners determine which block becomes the next official entry in the blockchain. This consensus mechanism prevents conflicting versions of the ledger and establishes a single authoritative history of transactions.
Chain Selection Rule
The Bitcoin network follows the “longest chain” rule, meaning that the valid chain is the one with the most accumulated Proof-of-Work. This ensures that miners cannot easily rewrite history, as they would need to outperform the collective computing power of the rest of the network.
Mining and Cryptographic Integrity
At the core of mining lies cryptographic assurance. Every block links back to the previous one through hash pointers, creating an immutable chain of records. Altering even a single transaction would invalidate all subsequent hashes, making tampering practically impossible without enormous computational resources.
Merkle Trees
Transactions within a block are organized into a Merkle tree. This structure allows efficient and secure verification of transactions. Instead of checking every transaction individually, nodes can use Merkle proofs to confirm inclusion with minimal data.
Cooling and Infrastructure in Mining Farms
Industrial mining farms are not only about computational capacity; they are also feats of engineering. The heat generated by ASIC hardware must be managed effectively to maintain efficiency and avoid damage.
Cooling Systems
- Air Cooling: Traditional fans and ventilation systems.
- Liquid Cooling: More advanced setups use dielectric liquids to submerge ASICs.
- Immersion Cooling: Entire racks submerged in specialized non-conductive fluids, maximizing efficiency.
Bitcoin Mining Rewards and Incentives
The incentive structure of mining has two pillars: block rewards and transaction fees. Together, they ensure miners remain motivated to contribute their computational power to the network.
Declining Rewards
As halvings reduce block rewards, transaction fees are expected to play a more prominent role in sustaining miner incentives. This gradual transition was part of the original design to align long-term incentives with network adoption.
The Global Hardware Supply Chain
Bitcoin mining hardware depends on specialized supply chains dominated by a handful of manufacturers. The majority of ASICs are produced in Asia, particularly in Taiwan and mainland China, where semiconductor fabrication capacity is concentrated.
Market Dynamics
ASIC demand follows Bitcoin’s price cycles. When prices rise, miners rush to expand capacity, creating supply shortages and long lead times. When prices fall, excess inventory floods the secondary market.
Bitcoin Mining and Game Theory
The resilience of the mining system is deeply rooted in game theory. Rational miners maximize profit by playing by the rules. Attempting to subvert the system would demand vast resources while likely reducing the value of their holdings.
51% Attack Theory
If a single entity controlled more than 50% of the hash rate, they could potentially reorganize the blockchain. However, the economic cost and market backlash make such an attack highly impractical in real-world conditions.
Orphaned Blocks and Forks
Sometimes, two miners solve the puzzle at nearly the same time, resulting in competing blocks. The network temporarily forks until one chain accumulates more Proof-of-Work, at which point the shorter chain is abandoned.
Orphaned Blocks
An orphaned block is a valid block that is not part of the main chain. While the miner loses the block reward, orphaned blocks highlight the competitive and probabilistic nature of mining.
Integration with Financial Markets
Today, mining is intertwined with broader financial systems. Publicly traded mining companies, institutional investment, and specialized financial instruments like hash rate futures connect mining economics with capital markets.
Listed Mining Companies
- Riot Platforms (NASDAQ: RIOT)
- Marathon Digital Holdings (NASDAQ: MARA)
- Hut 8 Mining Corp (NASDAQ: HUT)
Data Centers vs. Mining Farms
Although mining farms resemble data centers, there are significant differences. Data centers prioritize redundancy and uptime, while mining farms optimize for efficiency and raw computational power.
Comparison Table
| Aspect | Data Centers | Mining Farms |
|---|---|---|
| Primary Goal | Service delivery | Hash rate maximization |
| Infrastructure | High redundancy | Low-cost, efficiency-driven |
| Cooling | Air conditioning, advanced climate control | Air or immersion cooling focused on cost |
Bitcoin Mining and Open Source Software
The development of mining protocols and tools is heavily supported by open source communities. From mining pool protocols to monitoring dashboards, many of the innovations emerge from collaborative development.
Stratum Protocol
Most mining pools rely on the Stratum protocol, which standardizes communication between miners and pools. This protocol minimizes overhead and ensures efficient task distribution.
Future-Proofing Mining Infrastructure
While Bitcoin’s mining algorithm remains fixed to Proof-of-Work, the hardware and infrastructure supporting it continue to evolve. Mining operators adopt cutting-edge semiconductor designs, experiment with renewable energy integration, and scale operations globally.


