Stealth addresses were created to solve the fundamental privacy issues present in public blockchain systems.
| Key Fact | Summary |
|---|---|
| Purpose | Stealth addresses provide on-chain privacy by generating unique one-time destination addresses that decouple sender and receiver from the public transaction graph. |
| Unlinkability & Forward Privacy | Each payment uses a fresh address that cannot be linked to the recipient’s identity or past payments; even if a wallet is later deanonymized, prior transactions remain untraceable. |
| Cryptographic Basis | Built on elliptic-curve cryptography and ECDH to derive a shared secret from public information so the sender can create a one-time address without interacting with the recipient. |
| Key Components | Scan (view) key to detect incoming funds, spend key pair to claim them, and a publicly shared stealth meta-address from which one-time addresses are derived. |
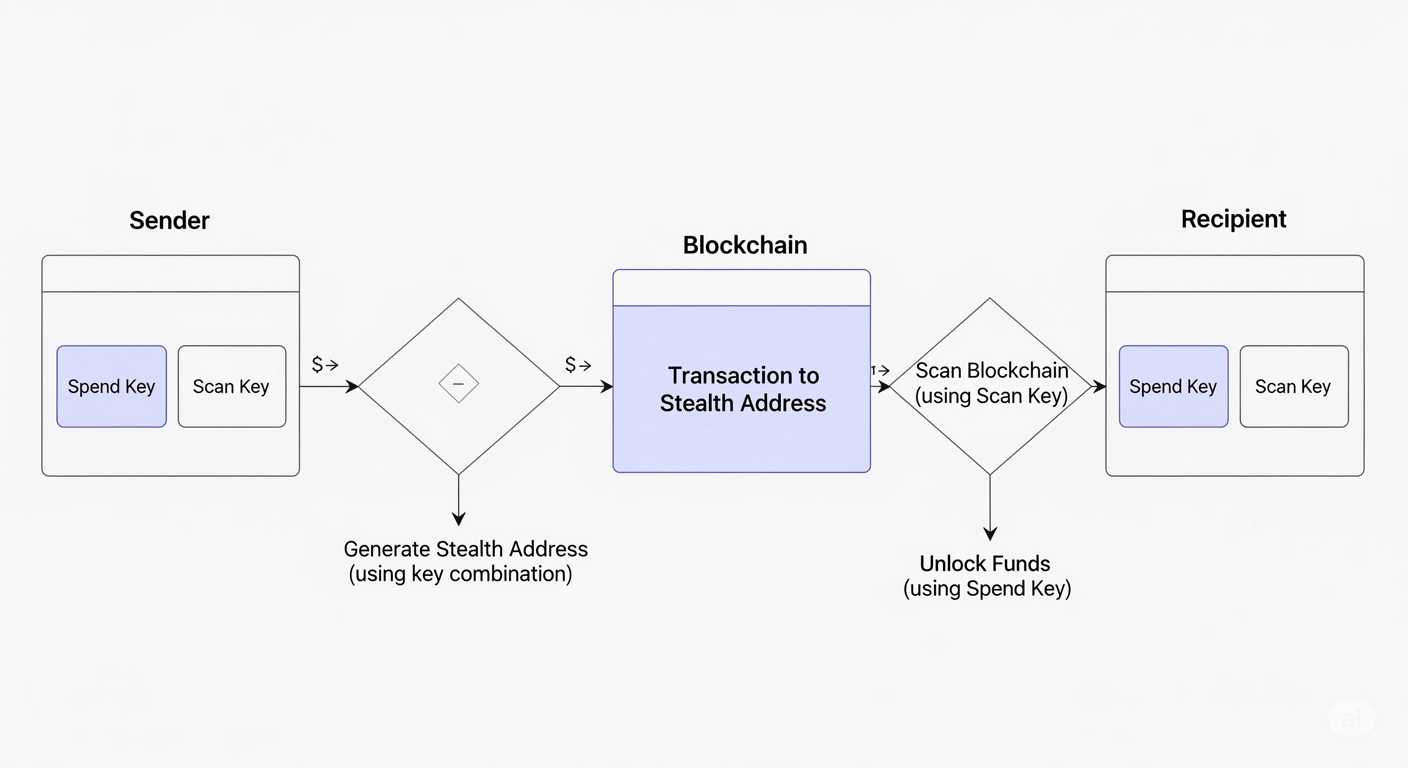
| High-Level Workflow | Recipient publishes meta-address → sender uses an ephemeral key and ECDH to generate a unique destination → funds are sent → recipient scans the chain and spends with the spend key. |
| Main Variants | BIP47 reusable payment codes (require a notification transaction) and Dual-Key Stealth Addresses (separate scan/view and spend keys so wallets can detect incoming payments without exposing spend keys). |
| Adoption in Monero | Monero uses dual-key stealth addresses (public view + public spend keys) combined with ring signatures and RingCT to make transfers unlinkable and amounts hidden. |
| On Ethereum & L2s | Account-based chains employ smart-contract solutions such as Umbra and zero-knowledge systems to enable stealth-like payments without modifying the base protocol. |
Why Stealth Addresses Were Invented
Public blockchains like Bitcoin and Ethereum operate transparently, which means every transaction is recorded and visible to anyone. While this openness supports trust and decentralization, it severely compromises user privacy. Anyone can trace funds from one address to another, leading to the possibility of identifying wallet owners, analyzing financial behavior, and even linking personal identities. This visibility has made cryptocurrencies pseudo-anonymous rather than truly private.
To address this, stealth addresses emerged as a way to decouple the sender and receiver from the public transaction graph. They allow users to receive payments through unique, one-time-use addresses, while keeping their identity and transaction history shielded from blockchain analysis tools.
Core Principles Behind Stealth Addresses
Unlinkability and Forward Privacy
The cornerstone of stealth addresses is unlinkability. Every transaction generates a unique address on the blockchain that cannot be linked back to the recipient’s actual wallet address. This ensures forward privacy — even if a recipient’s identity is revealed in the future, past transactions remain untraceable.
Asymmetric Cryptography
Stealth addresses use elliptic curve cryptography to derive one-time-use addresses from a publicly shared key. This cryptographic derivation enables any sender to create a unique address for a recipient without the recipient needing to interact or provide a new address.
How Stealth Addresses Work
To understand stealth addresses in practice, it’s essential to look at how keys are structured and how transactions are built.
Key Structure
| Component | Description |
|---|---|
| Scan Key | A public key used to detect incoming payments. |
| Spend Key | A private/public key pair used to claim the funds sent to a stealth address. |
| Stealth Address | Derived from the scan and spend keys; shared with the sender to receive funds. |
Transaction Flow
1. The recipient generates a stealth address from their scan and spend keys and publishes it.
2. The sender uses this address to generate a one-time destination address using ephemeral keys.
3. Funds are sent to this new address, and the recipient scans the blockchain for outputs matching their scan key.
4. When a match is found, the recipient uses their spend key to access the funds.
Variants of Stealth Addresses
Basic Stealth Addresses
These are the original implementation and are simple yet effective. However, they require the recipient to constantly scan the blockchain for transactions, which can be computationally expensive.
Reusable Payment Codes (BIP47)
Proposed in Bitcoin Improvement Proposal 47, this method introduces reusable payment codes. These codes allow the recipient to share one address publicly, while enabling the sender to create new, unlinkable addresses for each transaction. However, it still requires a notification transaction to be sent first.
Dual-Key Stealth Addresses (DKSA)
This variation enhances privacy and reduces scanning overhead. By using a second key pair (scan key), users can detect transactions without compromising the spend key. This is widely used in privacy coins such as Monero and has become a cornerstone of modern privacy architecture.
Stealth Addresses vs. Regular Addresses
| Feature | Stealth Address | Regular Address |
|---|---|---|
| Transaction Linkability | Unlinkable | Linkable |
| Public Visibility | Obfuscated | Fully Transparent |
| Scanning Requirement | Yes | No |
| Address Reusability | Yes (indirectly) | Yes (directly) |
Integration in Privacy Coins
Stealth addresses are a foundational privacy mechanism in many coins designed to prioritize anonymity. Most notably, Monero, one of the leading privacy coins, uses an advanced stealth address scheme to make every transaction unlinkable and untraceable.
In Monero, the dual-key stealth address system is paired with ring signatures and confidential transactions, creating a multi-layered privacy environment.
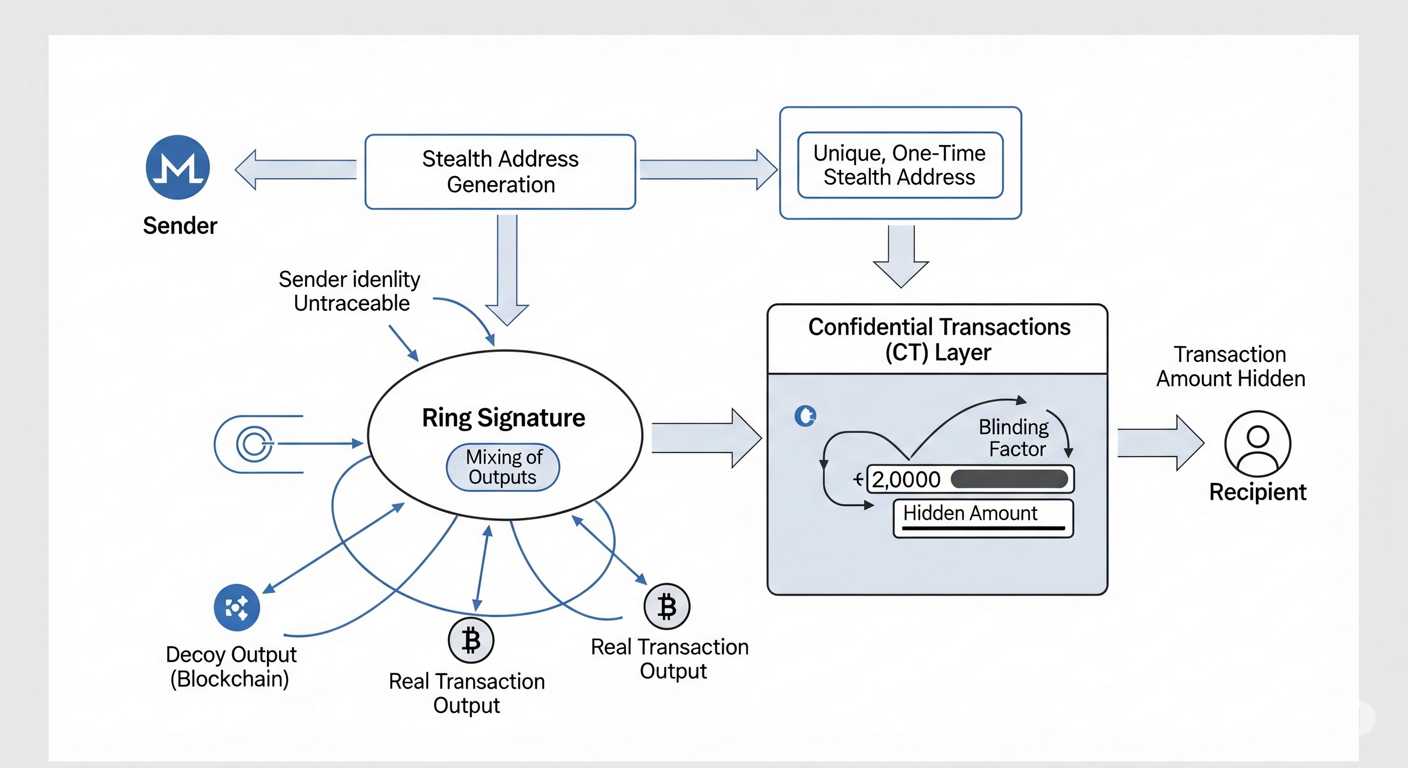
Monero’s Address Format
Each Monero address has two public keys: the public view key (scan key) and the public spend key. This duality allows Monero wallets to scan for incoming transactions and spend them securely without revealing any links.
Stealth Addresses in Ethereum and Beyond
Ethereum’s account-based model is different from Bitcoin’s UTXO model, making stealth address implementation more challenging. However, efforts like zk-SNARKs and zero-knowledge rollups are pushing boundaries in Ethereum’s privacy landscape.
Projects such as Umbra, developed by the Aztec team, are bringing stealth payments to Ethereum using cryptographic primitives. Instead of modifying the Ethereum core, these solutions are layered on top as smart contracts, which handle the creation of ephemeral addresses securely.
Umbra Protocol Workflow
| Step | Description |
|---|---|
| 1. Public Key Posting | User publishes a stealth meta-address on-chain. |
| 2. Encrypted Payload | Sender encrypts the recipient’s data using ECDH and broadcasts a transaction. |
| 3. Fund Retrieval | Recipient scans the chain, decrypts the payload, and claims the funds. |
Role of ECDH in Stealth Address Creation
Elliptic Curve Diffie-Hellman (ECDH) is the cryptographic basis of stealth address generation. It allows the sender and recipient to derive a shared secret without prior coordination. This secret is then used to generate a new one-time address for fund transfers.
Unlike traditional address sharing, ECDH avoids revealing any sensitive data, ensuring the transaction is untraceable and unlinkable.
Common Use Cases in Web3
Anonymous Donations
Stealth addresses enable activists, journalists, and non-profit organizations to receive donations without revealing their identity or transaction history. It prevents potential censorship and surveillance in politically sensitive environments.
Private Asset Transfers
In marketplaces or decentralized exchanges (DEXs), stealth addresses can obscure asset ownership and prevent adversaries from tracking users’ financial activities or front-running trades.
Secure NFT Transfers
Although NFTs are often public by design, stealth addresses can be used to privately transfer ownership without broadcasting the transaction link to observers. This is particularly useful in art auctions or tokenized real estate.
Challenges in Implementing Stealth Addresses
Blockchain Bloat and Computational Overhead
One technical drawback of stealth addresses is the increased computational load on the recipient, who must scan the blockchain to detect payments. This process may lead to performance issues, particularly on resource-limited devices like mobile wallets. The additional data also contributes to blockchain bloat, as more unique addresses are generated and stored on-chain.
Incompatibility with Light Clients
Stealth address systems often assume full node capabilities. This makes it difficult to integrate them into light clients, which don’t maintain a complete copy of the blockchain. As a result, wallets that aim to be lightweight or browser-based often avoid stealth address integration.
Lack of Native Support
Because stealth addresses aren’t universally supported across all blockchains or wallets, users often need to rely on external plugins, libraries, or smart contract systems. This fragmentation limits adoption and creates a barrier for interoperability in the Web3 ecosystem.
Stealth Addresses in Decentralized Finance (DeFi)
As DeFi platforms mature, the need for privacy-preserving transactions becomes more pressing. Transparent blockchains like Ethereum allow anyone to trace capital movement between protocols, wallets, and liquidity pools. This opens up strategic vulnerabilities in yield farming, arbitrage, and treasury management.
Stealth addresses, when integrated with DeFi protocols, help obscure user identities and transaction history, reducing attack vectors and market manipulation tactics.
Use in Lending Protocols
Privacy-centric lending platforms can use stealth addresses to allow users to borrow or repay funds anonymously, without exposing wallet balances or borrowing histories. This is especially important for whales and institutions who do not wish to reveal capital strategies.
Private Yield Farming
Yield strategies that rely on timing and execution can benefit from stealth addresses by preventing competitors from mimicking or counteracting positions. Stealth addresses allow each farming step to remain isolated on-chain.
Stealth Addresses and Multi-Signature Wallets
Integrating stealth addresses with multi-signature (multisig) wallets introduces complexity but also offers enhanced privacy for shared accounts. In standard setups, all participating public keys are visible, exposing organizational structures.
With stealth technology, a multisig wallet can construct hidden receiving addresses and keep the co-signers anonymous. Although difficult to implement, such functionality is being actively explored in DAO treasury management and corporate custody solutions.
Hardware Wallet Compatibility
Major hardware wallets like Ledger and Trezor do not natively support stealth addresses due to memory constraints and UI limitations. However, third-party tools or customized firmware versions can enable stealth functionalities when connected to full nodes or custom wallet software.
This means stealth address usage on hardware wallets often involves extra steps such as scanning transactions externally, importing view keys, or signing outputs manually. It reflects a growing need for hardware manufacturers to prioritize privacy features in next-gen devices.
Legal and Compliance Perspectives
While this article does not cover regulations in depth, it’s important to note that stealth addresses, though not illegal, often exist in a gray area depending on jurisdiction. Their ability to mask fund flows can make them controversial in regulated financial environments. That said, privacy is not synonymous with illegality. Many users adopt stealth addresses for purely personal and security-related reasons.
Developer Tools and SDKs
Libraries for Bitcoin and Ethereum
Developers interested in implementing stealth address functionality can use various open-source libraries such as:
- Libbitcoin: A powerful C++ toolkit that includes stealth address functionality.
- Umbra SDK: A JavaScript-based library built for Ethereum stealth transactions.
- Monero Wallet RPC: Exposes APIs for stealth scanning and private key access.
Testnets and Simulation
To experiment with stealth address features, developers can simulate transactions on public testnets like Ropsten (Ethereum) or Testnet3 (Bitcoin). Monero’s stagenet also allows for confidential testing with full stealth features enabled.
The Role of Stealth Addresses in Crypto Privacy Stack
Privacy in crypto is often composed of layered technologies. Stealth addresses are one component in a broader suite of privacy tools that include:
| Layer | Technology | Purpose |
|---|---|---|
| Network Layer | TOR, VPN, I2P | Hide IP address and location |
| Transaction Layer | Stealth Addresses | Obscure transaction links |
| Consensus Layer | RingCT, zk-SNARKs | Hide amounts and participants |
| Application Layer | Mixers, Private DEXs | Break traceability and logs |
This modular approach enables users to adopt privacy progressively depending on their risk profile and technical ability.
Educational Resources and User Guidance
For users interested in learning more about stealth addresses in practice, several tutorials and walkthroughs exist on developer and security platforms. Topics include wallet configuration, stealth payment tracking, and key management practices.
- Monero GUI Wallet: Offers an intuitive experience for stealth address use and fund recovery.
- Samourai Wallet: Known for privacy-first design with advanced coin control and address obfuscation tools.
- Wasabi Wallet: Incorporates CoinJoin and partial stealth techniques to prevent transaction clustering.
Understanding the Limitations of Pseudonymity
Even without stealth addresses, some users believe that blockchain addresses offer anonymity because they are not directly linked to real names. However, chain analysis firms use heuristics, address clustering, and transaction behavior to deanonymize wallets. Stealth addresses are one of the few countermeasures that actively resist such forensic techniques.
Thus, it is essential to differentiate between pseudonymity and privacy by design. The former is vulnerable to metadata correlation, while the latter leverages cryptographic principles to maintain true unlinkability.


