Conceived to keep private keys permanently offline and remove internet-born attack surfaces from day-to-day crypto operations, cold-storage reoriented how serious participants safeguard digital assets.
How Cold-Storage Fits Into Modern Crypto Operations
Cold-storage is best understood as an operational posture: keys are created, held, and used in an environment that never needs to touch a live network, while transaction construction and broadcasting happen elsewhere. Instead of chasing threats, the goal is to minimize exposure by design and build predictable, testable flows for spending and recovery. This separation between a “hot” environment (online wallet, exchange API, DeFi front end) and an “offline” signing enclave (hardware wallet, air-gapped workstation, or vault HSM) is what gives cold-storage its staying power among traders, long-term holders, treasurers, and funds.
Core Principles
- Isolation by default: keys are generated where they will live and never exported in the clear.
- Deterministic recovery: BIP-39 seed phrases and BIP-32 derivation paths allow reproducible wallet trees.
- Out-of-band approvals: human approvals, quorum rules, and physical access checks gate every spend.
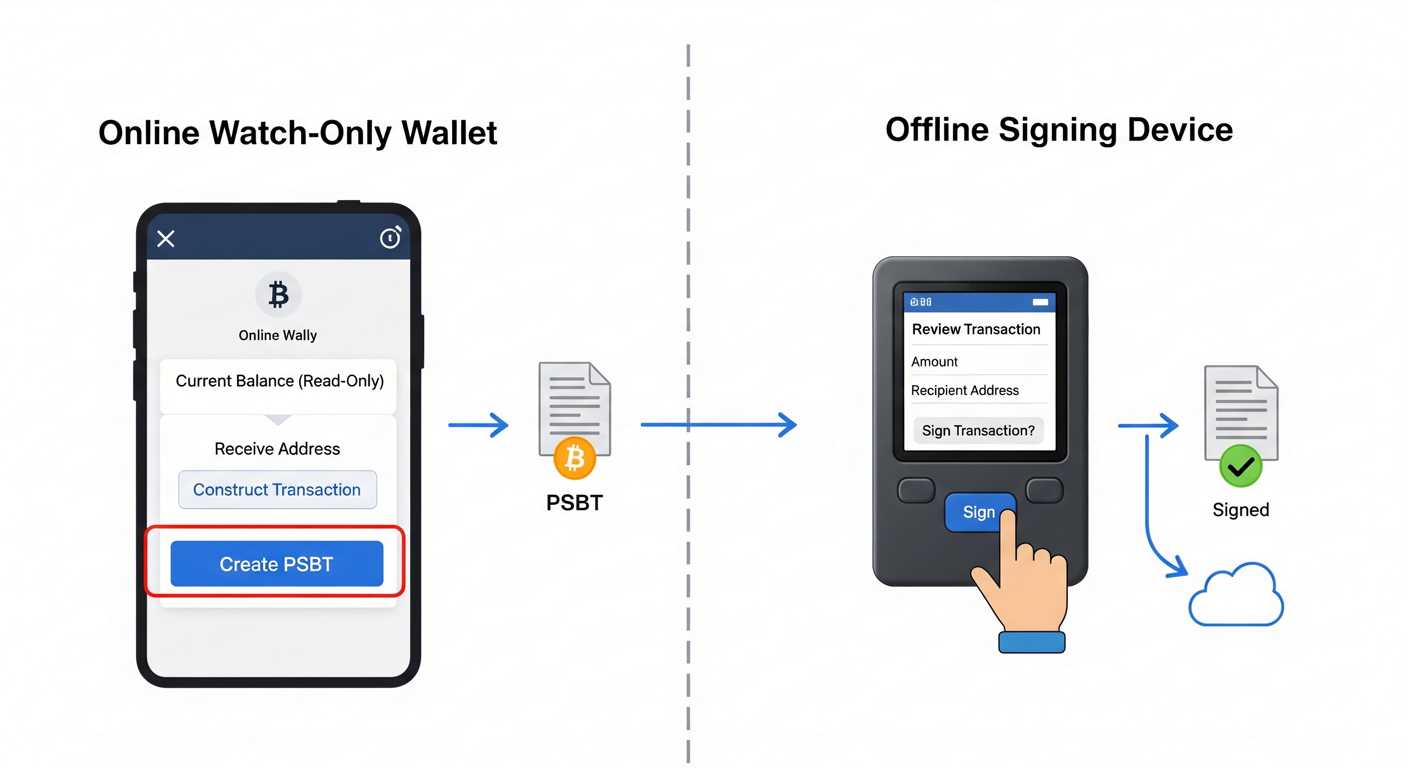
- Observable, not interactive: watch-only wallets observe balances and build transactions; offline signers only sign.
- Testability: dry-runs with small outputs, predictable change addresses, and logged workflows.
Cold-Storage Patterns You’ll See in Practice
| Pattern | Where Keys Live | Connectivity | How Signing Happens | Typical Use |
|---|---|---|---|---|
| Hardware Wallet (single-sig) | Secure element on a dedicated device | USB/Bluetooth; never exposes seed | Device signs; host passes unsigned tx | Self-custody, long-term holdings |
| Air-Gapped Workstation | Offline computer, no NICs or Wi-Fi | None; uses QR or microSD | PSBT loaded, signed, and exported | DIY custody, treasury workflows |
| Paper / Metal Backup (vaulted) | Seed phrase or xprv etched/stored | None; only for recovery | Rehydrate wallet when needed | Disaster recovery, inheritance |
| Multi-Sig Cold Vault | Multiple devices/shares in locations | Each signer isolated | Threshold signing across parties | Funds, DAOs, corporate treasuries |
| Institutional HSM | HSM modules in a secure facility | Controlled network inside vault | Policy-gated signing, audit logs | Exchanges, custodians, funds |
Air-Gapping and the Data Path
Air-gapping is the practice of keeping the signing environment physically disconnected from any network hardware. In cold-storage, this eliminates interactive channels, so only structured blobs flow in and out: an unsigned transaction goes in; a signature or signed transaction comes out. The transport can be a QR code, a microSD card, or typed hexadecimal—each is deliberate, inspectable, and one-way for the human operator.
Data Flow, Step by Step
- Discovery: a watch-only wallet monitors balances and UTXOs or account nonces.
- Construction: the online machine builds a transaction (Bitcoin PSBT, Ethereum EIP-155/EIP-1559 object, or EIP-712 typed data).
- Transfer to offline: move the unsigned payload via QR or removable media into the signer.
- Signing: the offline device verifies details on its screen and signs inside the enclave.
- Return path: the signature or signed payload goes back to the online machine to broadcast via a full node or gateway.

Key Lifecycle Without the Guesswork
A dependable cold-storage setup follows a clear lifecycle. Each phase is designed to be deliberate and repeatable, with artifacts you can audit later.
1) Generation
- Entropy: gather randomness from a device TRNG, optional dice rolls, or mixed sources; verify that the signer displays raw entropy and checksum if available.
- Seed & Paths: record the BIP-39 mnemonic and any BIP-39 passphrase; pin down BIP-32 paths (e.g., m/84’/0’/0′ for Bitcoin native segwit, m/44’/60’/0′ for Ethereum).
- Device Hardening: set PINs, enable duress pins if offered, and lock firmware versions after verification.
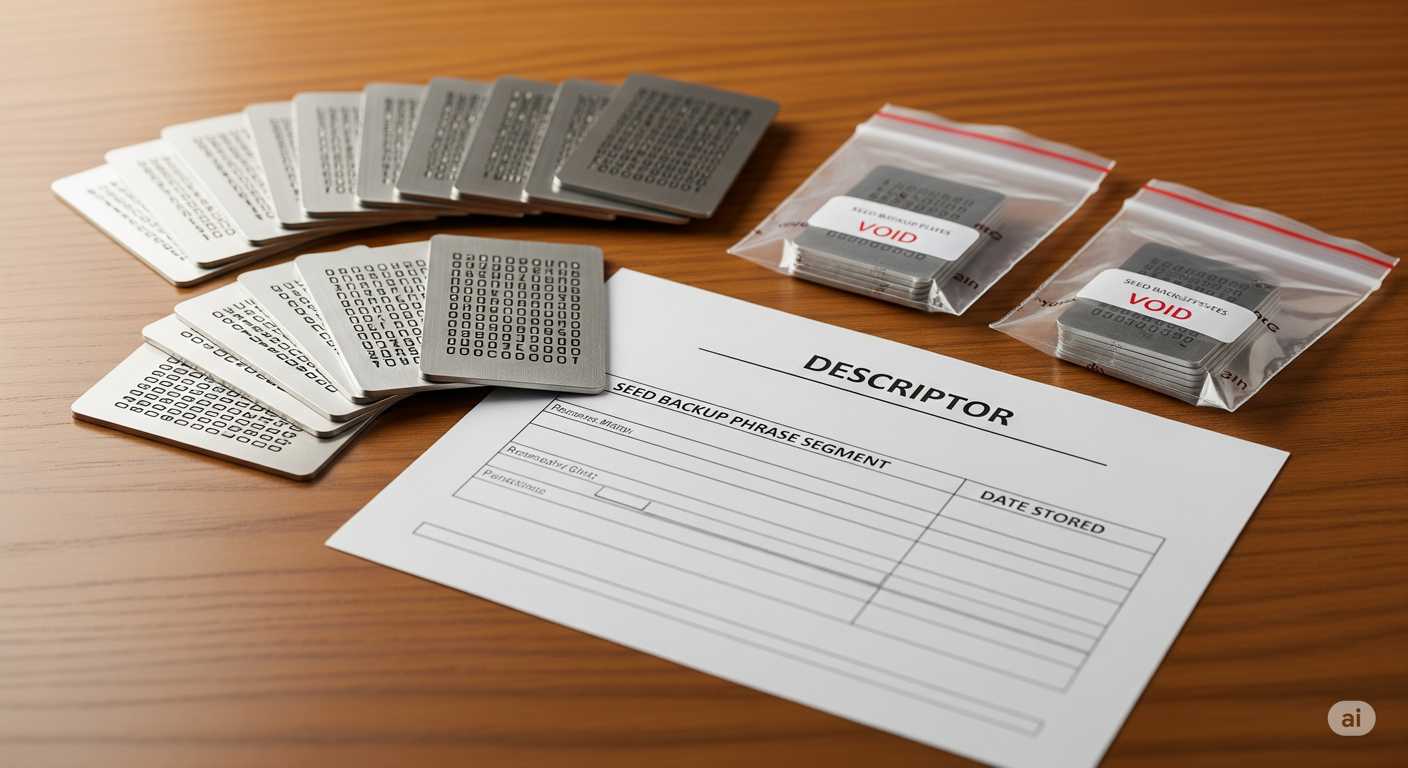
2) Storage
- Primary material: the seed never leaves the offline device except to a recovery medium.
- Recovery material: store seed or shares on durable media (metal plates, etched titanium) with tamper-evident envelopes.
- Geography: split locations to reduce single-site dependence, with a clear inventory and check-in cadence.
3) Use
- Watch-only views: xpubs or view keys let the online wallet track balances and build transactions.
- PSBT / Typed Data: prefer standard, checksum-bearing formats; inspect address, amount, change, and fee on the offline screen.
- Change discipline: send change to a known internal path; annotate addresses to avoid mix-ups.
4) Rotation & Retirement
- Periodic key rotation: move to a fresh seed on a set interval or after hardware events like firmware swaps.
- Decommissioning: wipe, verify wipe, and archive device IDs and logs; document final balances and derivation maps.
Standards That Make Cold-Storage Click
Several Bitcoin and Ethereum standards reduce ambiguity and make offline flows tractable across wallets and devices.
| Standard | What It Does | Why It Matters Offline |
|---|---|---|
| BIP-39 | Mnemonic seed phrases with checksum | Human-recordable recovery, portable to new devices |
| BIP-32 | Hierarchical deterministic derivation (xpub/xprv) | Watch-only on one side, signing on the other |
| BIP-44/49/84 | Path conventions for address types | Predictable addresses and change handling |
| BIP-174 (PSBT) | Portable partially signed Bitcoin transactions | Clean hand-offs via QR or microSD |
| EIP-155/1559 | Chain ID protections; fee fields for Ethereum | Safer cross-chain handling; explicit fee control |
| EIP-712 | Typed structured data signing | Readable domain-separated messages on device screens |
Hardware Wallets and Secure Elements
Purpose-built signing devices combine a microcontroller for the UI with a secure element that stores secrets and executes signing. The separation reduces the chances that general-purpose interfaces can view private key material. For a backgrounder on enterprise-grade modules related to this concept, see the hardware security module entry.
What To Look For in a Signer (Without Turning It Into a Shopping List)
- Clear signing screens: human-readable address, amount, and fees.
- Deterministic builds: reproducible firmware or vendor-verified hashes.
- QR workflows: camera-to-camera PSBT exchange to keep USB stacks out of scope.
- Open derivation disclosure: displays full path information and script type.
- Local passphrase entry: never typed on a networked host.

Air-Gapped Workstations for DIY Custody
Some operators build an offline signing computer from commodity parts: remove the Wi-Fi/Bluetooth module, omit Ethernet, disable all radios, and boot from read-only media. The trade is convenience for control—a general-purpose machine can run full-featured wallet software and review transaction details on a large display. When paired with PSBT and a camera-based workflow, it delivers the same core isolation as a dedicated device.
Minimal Build Checklist
- Hardware: desktop board with NIC physically removed, or a laptop with card pulled and antenna leads taped.
- Boot: live OS image on write-protected USB; keep a second USB for updates in a sealed bag.
- I/O: external webcam or smartphone to read QR codes; microSD reader for alternate transfer.
- Wallet software: one Bitcoin wallet with PSBT, one Ethereum wallet with offline signing mode.
Multi-Signature and Threshold Ideas
Cold-storage is frequently combined with threshold controls so that no single device or person can authorize a spend. The two most common patterns are Bitcoin script-level multisig and private-key-level secret splitting or multi-party computation.
Multisig (Script-Level)
Bitcoin lets you describe spending rules in script, e.g., “2 of these 3 keys must sign.” Each cosigner keeps a key in cold-storage; when spending, the online coordinator builds a PSBT and the offline devices each sign. The resulting transaction meets the script’s threshold when enough signatures are present.
Shamir and Friends (Key-Level)
Shamir’s Secret Sharing (SSS) splits a master secret into shares such that any subset of size t reconstructs it, and smaller subsets reveal nothing; many hardware wallets support this for seed backups.
| Dimension | Bitcoin Multisig | Secret Sharing / MPC |
|---|---|---|
| Where threshold lives | On-chain script or descriptor | In the secret itself (off-chain) |
| Offline posture | Each signer remains cold | Shares held on separate devices/locations |
| Chain visibility | May be explicit or masked (e.g., Taproot) | Appears as single-sig on-chain |
| Recovery behavior | Replace a lost signer with key rotation | Reconstruct from threshold of shares |
From “Watch-Only” to Signed Transaction
A reliable cold-storage routine has a predictable pipeline from a watch-only view to a broadcasted transaction. The watch-only wallet exposes balances, UTXO sets, and account nonces using public keys or xpubs—never private material. It constructs transactions with specific change outputs and fee strategies and then packages the unsigned payload for offline signing.
Bitcoin PSBT Flow
- Create: select inputs and outputs, specify change path, set fee rate; export a PSBT file/QR.
- Sign: on the offline signer, verify destination, change, and fee; sign inputs per policy.
- Finalize: combine signatures if multisig; produce a fully signed transaction hex.
- Broadcast: send via your node, a gateway, or a partner’s relay.
Ethereum Offline Flow
- Construct: set nonce, gas limit, and max fee fields (per EIP-1559), or prepare EIP-712 typed data.
- Sign: the offline signer displays the domain, chain ID, contract, and key fields.
- Submit: return the RLP-encoded signed payload to the online machine for broadcast.
Backups That Actually Rehydrate
Backups are useful only if you can reconstruct the exact wallet state on a new device. That requires more than a mnemonic: you also need derivation paths, script types, and any passphrases. For long-lived holdings, record these together in a sealed envelope or etched plate and maintain a registry that’s separate from the physical stash.
Backup Artifacts to Record
- Seed phrase: 12/24 words with checksum verified at creation time.
- Passphrase (if used): the 13th/25th word concept; store separately from the seed.
- Paths & descriptors: BIP-32 paths and, for Bitcoin, the output descriptor or wallet policy.
- Address lists: a small set of receiving addresses and change addresses for cross-checking.
- Device details: model, firmware hash, and any vendor-specific settings.
Operating a Treasury With Human-in-the-Loop Controls
Teams that hold funds for a DAO, foundation, or company often rely on cold-storage with multi-person approvals and clear separation of duties. The pattern is the same: keep keys offline, but add named roles, dual control, and logs that create a high-fidelity record of what happened and when.
Typical Roles
- Preparers: construct transactions on a watch-only wallet, attach memos, and propose outputs.
- Approvers: validate intent off-chain (board vote, multisig threshold) before any signing occurs.
- Signers: operate offline devices, verify on-screen details, and record serials and timestamps.
- Broadcasters: publish the signed transaction and archive the txid and receipts.
- Auditors: reconcile UTXOs/accounts, match proposals to signatures and broadcasts.
| Control | Mechanism | Offline Tie-In |
|---|---|---|
| Dual control | 2-of-N keys or two separate shares | Each signer on a distinct offline device |
| Policy windows | Schedules for when spends are allowed | Signers only operate during set windows |
| Spend caps | Per-tx and per-day thresholds | Device enforces display and approval |
| Address books | Pre-vetted destination lists | Display tags on offline screens |
The “Online Half” Still Matters
Even with perfectly isolated keys, the online workflow needs discipline. Run a full node when possible, so the transactions you build match your view of the chain. Keep fee estimation, UTXO selection, and address labeling deliberate; use descriptors to import wallet policies into your node or coordinator. The cold side can only attest to what’s on its screen; the online half is responsible for assembling the right ingredients.
Coordinator Hygiene
- Deterministic builds: prefer coordinators that publish hashes or reproducible builds.
- Descriptor imports: import wallet descriptors/xpubs; avoid ad-hoc address pools.
- Network isolation: route node traffic through a known pathway; keep signing separate.
A Note on “Air Gap” vs. “Air Gap-Like”
Some tools market one-way data diodes, restricted USB stacks, or sandboxed communication paths. The useful distinction is whether the signing enclave can be reached interactively over a live channel. In strictly air-gapped setups, the answer is no; all movement is mediated by static artifacts like QR frames or removable media.
UTXO and Account Models: Why Your Cold Flow Differs by Chain
Bitcoin’s UTXO model means each coin fragment is an input you must explicitly spend, and change returns to a new address path. Ethereum’s account model centers on a monotonically increasing nonce and stateful contracts. The offline signer needs to present the right details for each model so humans can review intent correctly.
| Aspect | Bitcoin (UTXO) | Ethereum (Account) |
|---|---|---|
| Primary review fields | Inputs, outputs, change, fee rate | To, value, gas, max fee, data |
| Offline transfer format | PSBT | RLP or EIP-712 typed data |
| Address derivation | BIP-84/86 paths, descriptors | m/44’/60’/… account paths |
| Human verification cue | Expected change path and tags | Contract name/domain and function |



